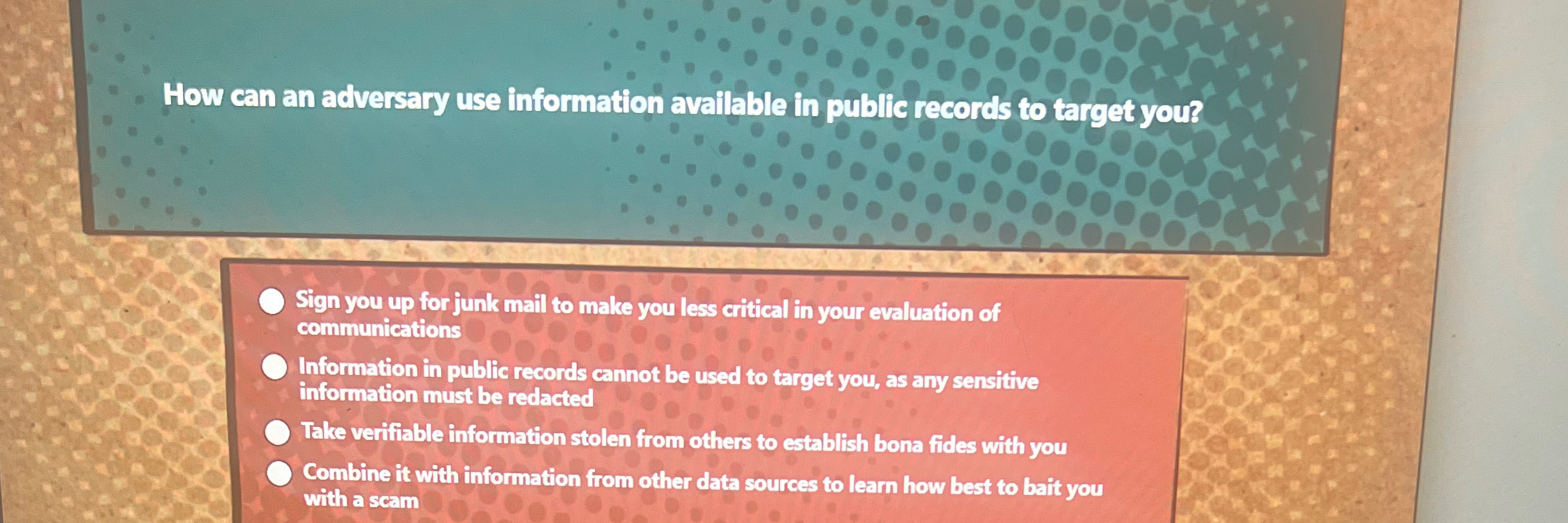
How Can Adversary Use Information Available - Information on programs, deployments, and response procedures. In this blog, we’ll explore how adversaries use publicly accessible data and what steps you can take to mitigate these risks. It is crucial to provide only. Combine it with information from other data sources to learn how best to bait you with a scam An adversary can use public records combined with other data sources to craft scams and target individuals. When adversaries are able to collect enough information, they can piece it. Learn how to protect your online identity, avoid cookies, compressed urls, and malicious code, and respond to identity theft and internet.
An adversary can use public records combined with other data sources to craft scams and target individuals. When adversaries are able to collect enough information, they can piece it. It is crucial to provide only. In this blog, we’ll explore how adversaries use publicly accessible data and what steps you can take to mitigate these risks. Combine it with information from other data sources to learn how best to bait you with a scam Information on programs, deployments, and response procedures. Learn how to protect your online identity, avoid cookies, compressed urls, and malicious code, and respond to identity theft and internet.
Combine it with information from other data sources to learn how best to bait you with a scam An adversary can use public records combined with other data sources to craft scams and target individuals. It is crucial to provide only. Information on programs, deployments, and response procedures. Learn how to protect your online identity, avoid cookies, compressed urls, and malicious code, and respond to identity theft and internet. In this blog, we’ll explore how adversaries use publicly accessible data and what steps you can take to mitigate these risks. When adversaries are able to collect enough information, they can piece it.
How Can An Adversary Use Information Available In Public Records
It is crucial to provide only. In this blog, we’ll explore how adversaries use publicly accessible data and what steps you can take to mitigate these risks. When adversaries are able to collect enough information, they can piece it. Combine it with information from other data sources to learn how best to bait you with a scam Information on programs,.
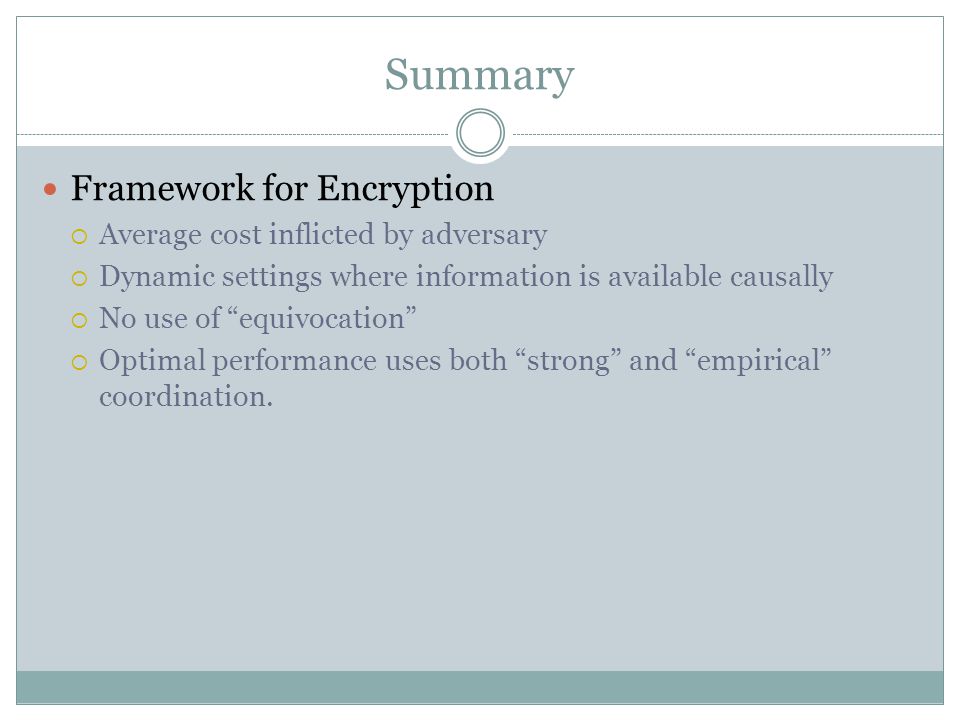
Operational Security Awareness ppt video online download
An adversary can use public records combined with other data sources to craft scams and target individuals. Combine it with information from other data sources to learn how best to bait you with a scam It is crucial to provide only. When adversaries are able to collect enough information, they can piece it. Learn how to protect your online identity,.
How Can An Adversary Use Information Available In Public Quizlet
It is crucial to provide only. When adversaries are able to collect enough information, they can piece it. Information on programs, deployments, and response procedures. In this blog, we’ll explore how adversaries use publicly accessible data and what steps you can take to mitigate these risks. Learn how to protect your online identity, avoid cookies, compressed urls, and malicious code,.
Presentation Objectives ppt download
Information on programs, deployments, and response procedures. Combine it with information from other data sources to learn how best to bait you with a scam It is crucial to provide only. An adversary can use public records combined with other data sources to craft scams and target individuals. When adversaries are able to collect enough information, they can piece it.
Torbutton and Firefox Mike Perry Mozilla Brown Bag Jun 22, ppt download
Information on programs, deployments, and response procedures. When adversaries are able to collect enough information, they can piece it. In this blog, we’ll explore how adversaries use publicly accessible data and what steps you can take to mitigate these risks. Learn how to protect your online identity, avoid cookies, compressed urls, and malicious code, and respond to identity theft and.
PAUL CUFF ELECTRICAL ENGINEERING PRINCETON UNIVERSITY Secure
Learn how to protect your online identity, avoid cookies, compressed urls, and malicious code, and respond to identity theft and internet. It is crucial to provide only. Information on programs, deployments, and response procedures. Combine it with information from other data sources to learn how best to bait you with a scam When adversaries are able to collect enough information,.
Solved How can an adversary use information available in
It is crucial to provide only. In this blog, we’ll explore how adversaries use publicly accessible data and what steps you can take to mitigate these risks. Combine it with information from other data sources to learn how best to bait you with a scam Information on programs, deployments, and response procedures. An adversary can use public records combined with.
How Can An Adversary Use Information Presentation Objectives Ppt Download
An adversary can use public records combined with other data sources to craft scams and target individuals. It is crucial to provide only. In this blog, we’ll explore how adversaries use publicly accessible data and what steps you can take to mitigate these risks. Combine it with information from other data sources to learn how best to bait you with.
How Can an Adversary Use Information Available in Public Records to
It is crucial to provide only. In this blog, we’ll explore how adversaries use publicly accessible data and what steps you can take to mitigate these risks. An adversary can use public records combined with other data sources to craft scams and target individuals. When adversaries are able to collect enough information, they can piece it. Learn how to protect.
Solved How can an adversary use information available in public
In this blog, we’ll explore how adversaries use publicly accessible data and what steps you can take to mitigate these risks. Information on programs, deployments, and response procedures. Combine it with information from other data sources to learn how best to bait you with a scam When adversaries are able to collect enough information, they can piece it. Learn how.
It Is Crucial To Provide Only.
Combine it with information from other data sources to learn how best to bait you with a scam Learn how to protect your online identity, avoid cookies, compressed urls, and malicious code, and respond to identity theft and internet. In this blog, we’ll explore how adversaries use publicly accessible data and what steps you can take to mitigate these risks. An adversary can use public records combined with other data sources to craft scams and target individuals.
Information On Programs, Deployments, And Response Procedures.
When adversaries are able to collect enough information, they can piece it.