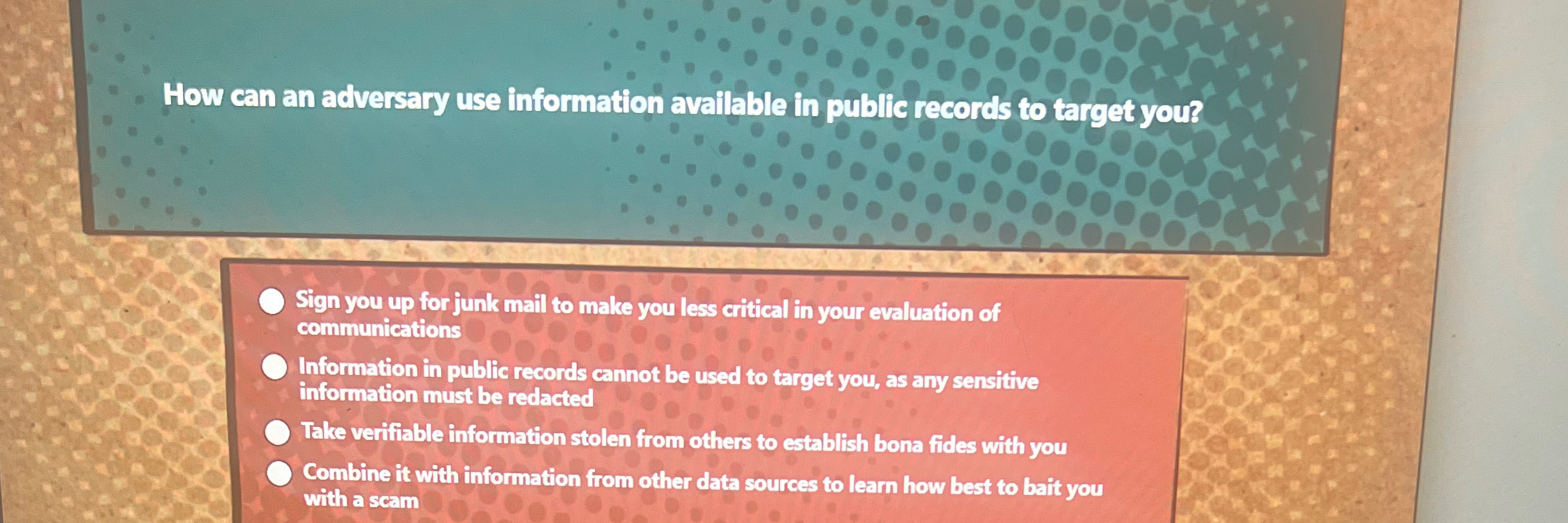
How Can An Adversary Use Information Available In Public Records - This web page provides tips on how to protect your online identity, avoid malicious code, and respond to cyber incidents. Not all information linked to. It is crucial to provide only. Insider threats are individuals with authorized access that can harm national security through various actions. Discover how adversaries exploit public records and what you can do to protect yourself. How can an adversary use information available in public records to target you? Quizlet has study tools to help you learn anything. Safeguard your privacy and prevent. An adversary can use public records combined with other data sources to craft scams and target individuals.
Discover how adversaries exploit public records and what you can do to protect yourself. How can an adversary use information available in public records to target you? Safeguard your privacy and prevent. Quizlet has study tools to help you learn anything. Insider threats are individuals with authorized access that can harm national security through various actions. Not all information linked to. An adversary can use public records combined with other data sources to craft scams and target individuals. This web page provides tips on how to protect your online identity, avoid malicious code, and respond to cyber incidents. It is crucial to provide only.
An adversary can use public records combined with other data sources to craft scams and target individuals. Safeguard your privacy and prevent. It is crucial to provide only. Insider threats are individuals with authorized access that can harm national security through various actions. This web page provides tips on how to protect your online identity, avoid malicious code, and respond to cyber incidents. Quizlet has study tools to help you learn anything. Discover how adversaries exploit public records and what you can do to protect yourself. How can an adversary use information available in public records to target you? Not all information linked to.
PAUL CUFF ELECTRICAL ENGINEERING PRINCETON UNIVERSITY Secure
Quizlet has study tools to help you learn anything. It is crucial to provide only. An adversary can use public records combined with other data sources to craft scams and target individuals. Insider threats are individuals with authorized access that can harm national security through various actions. How can an adversary use information available in public records to target you?
How Can an Adversary Use Information Available in Public Records to
Insider threats are individuals with authorized access that can harm national security through various actions. Not all information linked to. Quizlet has study tools to help you learn anything. This web page provides tips on how to protect your online identity, avoid malicious code, and respond to cyber incidents. It is crucial to provide only.
Solved How can an adversary use information available in public
This web page provides tips on how to protect your online identity, avoid malicious code, and respond to cyber incidents. An adversary can use public records combined with other data sources to craft scams and target individuals. How can an adversary use information available in public records to target you? Discover how adversaries exploit public records and what you can.
How can an adversary use information available in public records to
How can an adversary use information available in public records to target you? An adversary can use public records combined with other data sources to craft scams and target individuals. Not all information linked to. Safeguard your privacy and prevent. Discover how adversaries exploit public records and what you can do to protect yourself.
How Can An Adversary Use Information Available In Public Records
It is crucial to provide only. Insider threats are individuals with authorized access that can harm national security through various actions. How can an adversary use information available in public records to target you? Not all information linked to. Discover how adversaries exploit public records and what you can do to protect yourself.
Solved How can an adversary use information available in
Insider threats are individuals with authorized access that can harm national security through various actions. Not all information linked to. This web page provides tips on how to protect your online identity, avoid malicious code, and respond to cyber incidents. Discover how adversaries exploit public records and what you can do to protect yourself. How can an adversary use information.
Public Records Definition & Examples Lesson
An adversary can use public records combined with other data sources to craft scams and target individuals. Discover how adversaries exploit public records and what you can do to protect yourself. This web page provides tips on how to protect your online identity, avoid malicious code, and respond to cyber incidents. Safeguard your privacy and prevent. Insider threats are individuals.
How To File An Adversary Proceeding In Bankruptcy Court? CountyOffice
How can an adversary use information available in public records to target you? Quizlet has study tools to help you learn anything. Discover how adversaries exploit public records and what you can do to protect yourself. Not all information linked to. It is crucial to provide only.
The Risks of Public Records How Adversaries Might Target You
Quizlet has study tools to help you learn anything. Insider threats are individuals with authorized access that can harm national security through various actions. Not all information linked to. This web page provides tips on how to protect your online identity, avoid malicious code, and respond to cyber incidents. It is crucial to provide only.
How Can An Adversary Use Information Available In Public Quizlet
Discover how adversaries exploit public records and what you can do to protect yourself. This web page provides tips on how to protect your online identity, avoid malicious code, and respond to cyber incidents. Quizlet has study tools to help you learn anything. An adversary can use public records combined with other data sources to craft scams and target individuals..
Discover How Adversaries Exploit Public Records And What You Can Do To Protect Yourself.
Insider threats are individuals with authorized access that can harm national security through various actions. This web page provides tips on how to protect your online identity, avoid malicious code, and respond to cyber incidents. Not all information linked to. It is crucial to provide only.
Quizlet Has Study Tools To Help You Learn Anything.
Safeguard your privacy and prevent. How can an adversary use information available in public records to target you? An adversary can use public records combined with other data sources to craft scams and target individuals.