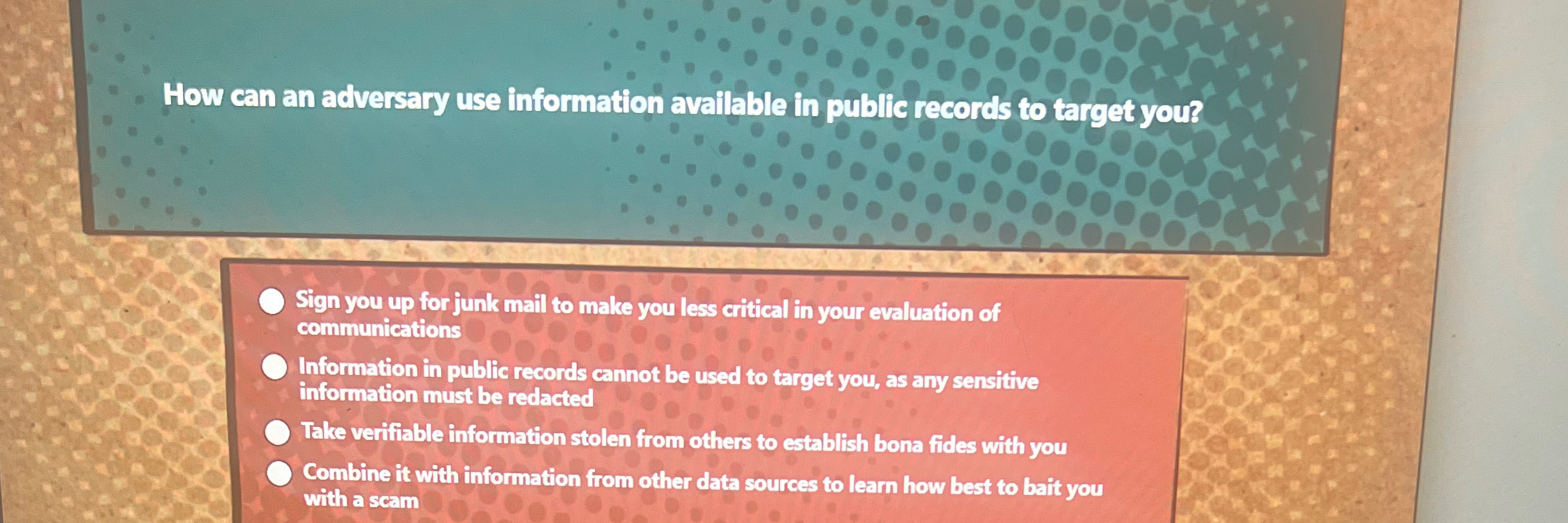
How Can An Adversary Use Information Available In Public - It is crucial to provide only. Public records can be used by adversaries to target individuals by establishing trust, tailoring scams, and overwhelming with junk mail. How can an adversary use information available in public records to target you? An adversary can use public records combined with other data sources to craft scams and target individuals. Combine it with information from other data sources to learn how best to bait you with a scam Quizlet has study tools to help you learn anything. Malicious code can do damage by corrupting files, encrypting or erasing your hard drive, and/or allowing hackers access.
Combine it with information from other data sources to learn how best to bait you with a scam It is crucial to provide only. How can an adversary use information available in public records to target you? Malicious code can do damage by corrupting files, encrypting or erasing your hard drive, and/or allowing hackers access. An adversary can use public records combined with other data sources to craft scams and target individuals. Quizlet has study tools to help you learn anything. Public records can be used by adversaries to target individuals by establishing trust, tailoring scams, and overwhelming with junk mail.
Malicious code can do damage by corrupting files, encrypting or erasing your hard drive, and/or allowing hackers access. It is crucial to provide only. How can an adversary use information available in public records to target you? Public records can be used by adversaries to target individuals by establishing trust, tailoring scams, and overwhelming with junk mail. Combine it with information from other data sources to learn how best to bait you with a scam Quizlet has study tools to help you learn anything. An adversary can use public records combined with other data sources to craft scams and target individuals.
How Can An Adversary Use Information Available In Public Records
Quizlet has study tools to help you learn anything. Malicious code can do damage by corrupting files, encrypting or erasing your hard drive, and/or allowing hackers access. How can an adversary use information available in public records to target you? Public records can be used by adversaries to target individuals by establishing trust, tailoring scams, and overwhelming with junk mail..
How can an adversary use information available in public records to
Public records can be used by adversaries to target individuals by establishing trust, tailoring scams, and overwhelming with junk mail. It is crucial to provide only. Malicious code can do damage by corrupting files, encrypting or erasing your hard drive, and/or allowing hackers access. An adversary can use public records combined with other data sources to craft scams and target.
EFFECTIVE DETECTIVE Presented for February 22, 2017 Presented By
Quizlet has study tools to help you learn anything. Combine it with information from other data sources to learn how best to bait you with a scam Public records can be used by adversaries to target individuals by establishing trust, tailoring scams, and overwhelming with junk mail. Malicious code can do damage by corrupting files, encrypting or erasing your hard.
How Can An Adversary Use Information Available In Public Quizlet
Public records can be used by adversaries to target individuals by establishing trust, tailoring scams, and overwhelming with junk mail. How can an adversary use information available in public records to target you? Quizlet has study tools to help you learn anything. Combine it with information from other data sources to learn how best to bait you with a scam.
How Can an Adversary Use Information Available in Public Records to
It is crucial to provide only. Combine it with information from other data sources to learn how best to bait you with a scam An adversary can use public records combined with other data sources to craft scams and target individuals. Malicious code can do damage by corrupting files, encrypting or erasing your hard drive, and/or allowing hackers access. Quizlet.
Solved How can an adversary use information available in public
Public records can be used by adversaries to target individuals by establishing trust, tailoring scams, and overwhelming with junk mail. Quizlet has study tools to help you learn anything. Malicious code can do damage by corrupting files, encrypting or erasing your hard drive, and/or allowing hackers access. How can an adversary use information available in public records to target you?.
COSC 316 Host Computer Security ppt download
Combine it with information from other data sources to learn how best to bait you with a scam Public records can be used by adversaries to target individuals by establishing trust, tailoring scams, and overwhelming with junk mail. Quizlet has study tools to help you learn anything. An adversary can use public records combined with other data sources to craft.
Solved How can an adversary use information available in
How can an adversary use information available in public records to target you? Public records can be used by adversaries to target individuals by establishing trust, tailoring scams, and overwhelming with junk mail. Combine it with information from other data sources to learn how best to bait you with a scam It is crucial to provide only. An adversary can.
Presentation Objectives ppt download
How can an adversary use information available in public records to target you? Quizlet has study tools to help you learn anything. Combine it with information from other data sources to learn how best to bait you with a scam Malicious code can do damage by corrupting files, encrypting or erasing your hard drive, and/or allowing hackers access. It is.
The Risks of Public Records How Adversaries Might Target You
Combine it with information from other data sources to learn how best to bait you with a scam It is crucial to provide only. An adversary can use public records combined with other data sources to craft scams and target individuals. Public records can be used by adversaries to target individuals by establishing trust, tailoring scams, and overwhelming with junk.
It Is Crucial To Provide Only.
Combine it with information from other data sources to learn how best to bait you with a scam An adversary can use public records combined with other data sources to craft scams and target individuals. Public records can be used by adversaries to target individuals by establishing trust, tailoring scams, and overwhelming with junk mail. Malicious code can do damage by corrupting files, encrypting or erasing your hard drive, and/or allowing hackers access.
How Can An Adversary Use Information Available In Public Records To Target You?
Quizlet has study tools to help you learn anything.